More than 1500 posgresql servers are at risk in the cryptocurrency mining campaign without threads
Open Postgresql counterparts are the goal of an ongoing campaign designed for unauthorized access and deployment of cryptocurrencies.
The Wiz Cloud Security Company said that the activity is a variable of the infiltration group that was marked for the first time by Aqua Security in August 2024, which included the use of the malware of the harmful programs that it is called pg_mem. The campaign was attributed to Wiz’s threatening actor paths like Jinx-0126.
“The representative of the threat has evolved since then, as he has implemented defense evasion techniques such as spreading diodes with a unique fragmentation for each goal and implementing the top of the lead mine – it is likely to evade the disclosure of [cloud workload protection platform] Solutions that depend only on retail reputation, “Avigayil mechtinger, Yaara Shriki and Gili Tikochinski He said.
Wiz also revealed that the campaign has most likely claimed more than 1500 victims, indicating that the posgresql counterparts exposed to the public with weak or predictable credentials prevailing enough to become a target to attack the opportunists for opportunistic threats.
The most distinctive aspect of the campaign is the misuse of the version … from the SQL program to implement the Shell Arbitous orders on the host.
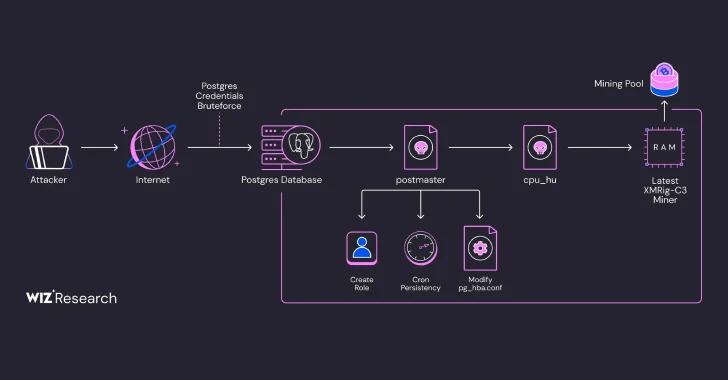
The access provided by the successful exploitation of Postgresql services that have been used weak to conduct the initial survey and drop the encrypted Base64 load, which, in fact, is a text of a shell that kills the workers of the cryptocurrency workers and drops a duo called PG_Core.
It was also downloaded on the server is the director of the Golag Binary Office Imitate Postgresql user database server. It is designed to prepare stability on the host using CRON, creating a new role with high privileges, and another dual writing called CPU_HU on the disk.
CPU_HU, for its part, download the latest version of Xmrig miner From GitHub and launches it without imagination through the known Linux technology referred to MEMFD.
“The representative of the threat appoints a unique mining worker for every victim,” Wiz said, adding that he identified three different portfolios linked to the threat representative. “Each portfolio had approximately 550 workers. Completely, this indicates that the campaign could have benefited more than 1500 machines.
https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEi7T76r7kS8PZOsdzi_Rqfb4YQ9TlduBV_oDyqzjBXyrvuLrPjXBthb3OjCYCE8xTnq1h84I8Wfzxt9-v1kK-7lVj1YsxCoxZY8zZIM9knp_wY0_ZAsCQsLz2mUol-4MKoKsTvrZd9W04c39ORJP9qsWlAOeL3a9uhaSaO0cuZ3LC2KRz01mXOTrKxMFccD/s728-rw-e365/main-crypto.jpg




